Table of Contents
Securing CLI access with MFA through AWS IAM Identity Center
Published on:
Use Case
The intention behind this setup is to use the aws clie more frequently. However,
I don’t want to store my aws_access_key_id and aws_secret_access_key
in a plain text file on my computer. Additionally, I want to use a hardware
security key to ensure the same level of protection for the aws cli as
for the web console.
The AWS cli currently does not support FIDO2 security tokens for IAM users natively. Hardware security keys are only supported if they can perform OATH authentication1. Since my Yubikey has not configuration slot left for OATH authentication, this I cannot configure my Yubikey for OATH authentication. Luckily, AWS offers an alternative.
The alternative is using AWS IAM Identity Center to create and manage users instead of using IAM users. This allows the use of FIDO2 based security tokens.
Enabling AWS IAM Identity Center
To configure AWS IAM Identity Center users, it is necessary to enable the AWS IAM Identity Center first2. AWS recommends to enable it with AWS Organizations. Since there are no costs associated with using AWS Organizations, I followed the recommendation.
AWS IAM Identity Center uses so called Identity sources for managing users
and groups. Such Identity sources could be an Azure Active Directory or
other third party identity providers. AWS also offers an integrated Identity
source called Identity Center directory. Since I do not want to use
an additional third party Identity source, I go with the builtin one.
Configuring an AWS IAM Identity Center user
To configure an AWS IAM Identity Center user it is required to login to the AWS web console with either the account root user or with a configured IAM user that has sufficient permissions.
After logging in to the web console, I have to open the IAM Identity Center console3. The AWS documentation is very good on this topic and therefore I refrain from listing it here again. The general process of creating a user is as follows:
- Create a user via the IAM Identity Center console.
- Add a group to the IAM Identity Center console.
- Create appropriate permissions that can be assigned to the created group.
- Add the user to the group.
Once the user is created, an email is sent to the email address of this user. This email contains the link that can be used to set a password for the account. After completing the initial account setup, I get redirected to the AWS console.
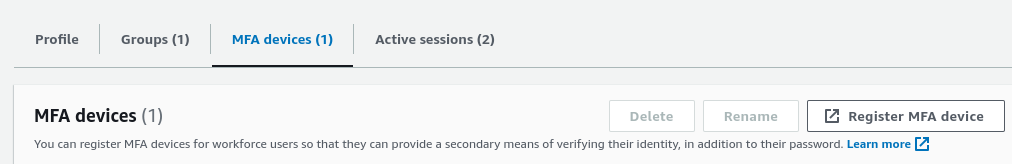
The next step is to configure the MFA device. Either, AWS asks you
to configure a MFA device directly after the initial password of the
users is configured or you have to initiate it manually. If a MFA device
has to be registered manually, the user object within IAM Identity Center
must be selected. On the detail page of the selected user, is a
tab called MFA devices. After selecting the tab, the button to
register a MFA device is shown.
Note: AWS IAM Identity Center users do not login via the regular AWS login url. The url which AWS IAM Identity Center users must use is displayed in the IAM Identity Center dashboard in the
Settings summarybox at the right of the window. The url has the format https://d-xxxxxxxxxx.awsapps.com/start.
Once the MFA device is setup successfully, the integration of the aws cli and AWS CLI IAM Identity Center can be configured.
Integrate AWS CLI with IAM Identity Center
AWS offers a good documentation on how to integrate the CLI with the
IAM Identity Center4. A prerequisite is to have the aws cli installed
on the system. The configuration of the cli is done via aws configure sso.